Author: Pinak Team
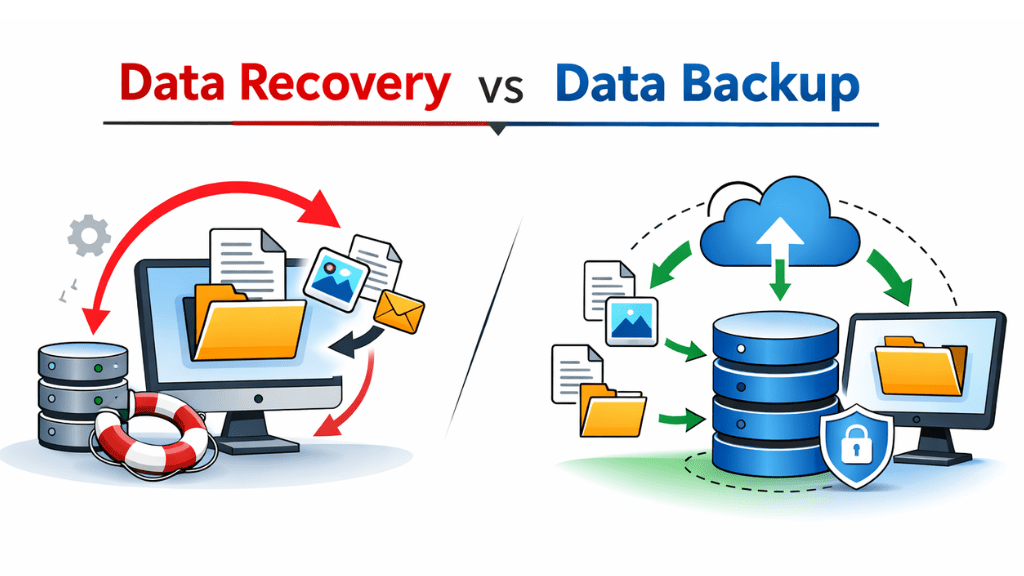
Data Recovery vs Data Backup: Every Business Must Know
Every business today runs on data. Client records, financial files, emails, project documents, designs, databases. When that data is safe, operations run smoothly. When it is lost, everything slows down or even stops. Many professionals use the terms Data Recovery and Data Backup as if they mean the same thing. They do not. Understanding the…

10 Essential Tips for Safely Using Public Wi-fi
Almost all of us use public Wi-Fi. We sit in a cafe, order coffee, ask for the password, and connect within seconds. At airports, malls, hotels, even parks, free internet feels normal now. It saves mobile data and helps us stay connected. But here is the truth most people ignore. Public Wi-Fi is one of…

How Does SSL Certificate Work and types of SSL certificates?
To understand how SSL certificate work, think about the last time you entered your password, card number, or email on a website. You probably did not stop to wonder whether that information was safe or not. You just trusted the site and went ahead with it. That trust comes from one small thing you often…

5 Cyber Security Tips to Secure Your Website from Cyber Attacks
Most businesses now run through their website. It stores customer details, handles payments, collects inquiries, and represents your brand online. Yet these same sites draw attacks more than ever before. Hackers do not care if you are new or big; size offers no shield anymore. Many times, cyber criminals target small and medium websites because…

National Cyber Strategy and Federal Policy Shifts
Cybersecurity has quietly evolved from a concern within operations to a national level. Something that once existed within information technology and security groups is now influencing conversations at the executive table and within government and regulatory settings. In a global context, national cyber-strategies are in a state of rapid evolution, and thus, so are the…

Ransomware Evolution: Commoditization and Geopolitical Expansion
Five years ago, cases involving ransomware attacks were viewed as one-off occurrences; that is, a hospital would be attacked, the incident would go around, and people would go on with their lives. Ransomware attacks today become more pervasive as they target organizations across sectors and regions. Not only has the number of attacks changed, but…